Hi,
I was testing a website exclusion in Intercept-X and had a hard time to finnaly get it working.
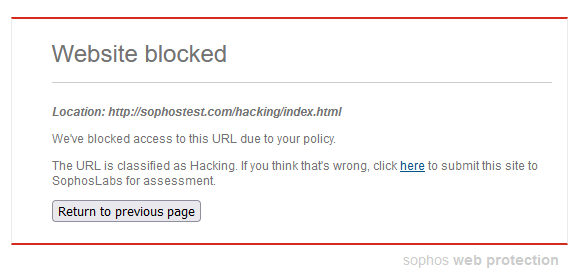
So I wanted to browse to the Sophos Testsite.
As expected this was blocked. regardless of http or https used.
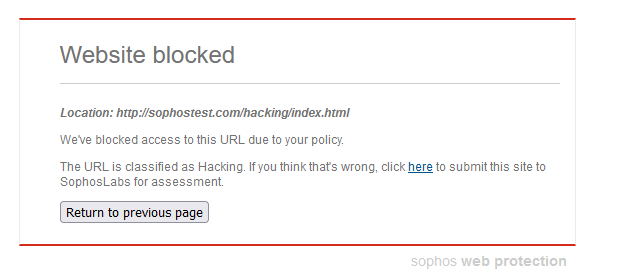
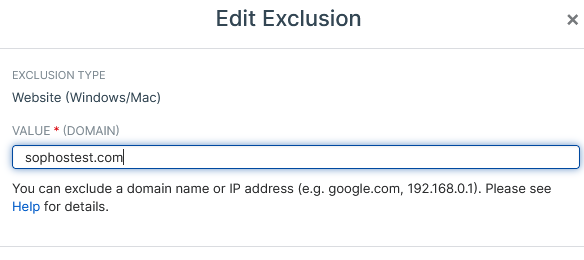
So I went to Central Global settings and created an exception for that website and selected a manual Category:
But I Intercept-X was still blocking access to the page.
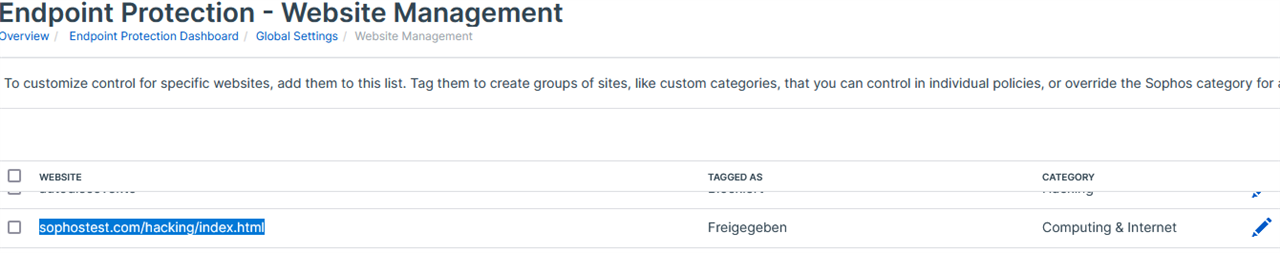
Ruling out a specific module, I disabled one by one.
Obviously it was beeing blocked by Sophos Network Threat Protection.
The machine has EAP installed and https decryption enabled.

I could immediately browse to that website after disabling Sophos Network Threat Protection.
So I added the second exception for the website in the https decryption section:

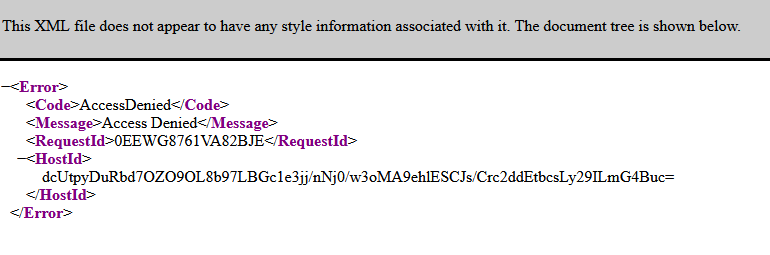
Now, if I open that page with https I can only see xml code:
http still shows block banner
So I added a third exception in the Threat Policy for the device:
but this did not change anything.
I don't have a clue where to allow it else than on the three menues I already was.
This thread was automatically locked due to age.

