Hello all,
I'm running an XG at my home and have an Ubuntu 20.04 host in a datacenter running strongswan ipsec. We are unable to make a basic IPSEC site-to-site connection. I have a server inside my home also running Ubuntu, and we can make the connection that way using port forwarding and basic firewall rules. We would like to connect my XG to my Ubuntu server instead. I know that the XG is running strongswan too, as that is the defacto IPSEC deployment method for Linux.
Questions:
- Is this possible?
- Where are the IPSEC logs?
- Which encryption methods are used in the XG IPSEC configuration?
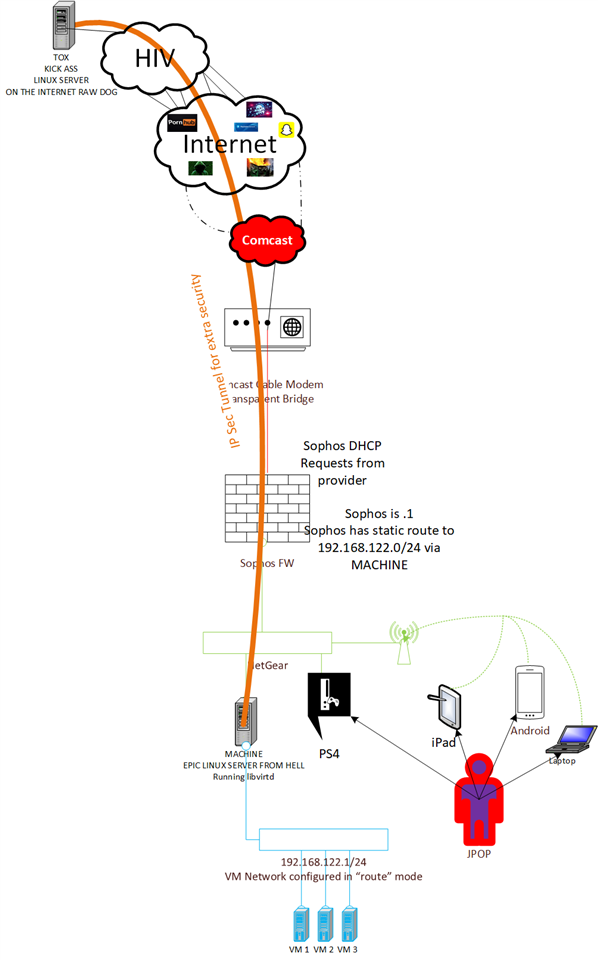
I drew a crude document diagram of what we are trying to achieve if it is needed.
 |
Jeff
This thread was automatically locked due to age.


