Hi all,
We've been running an updated behavioral engine in the early access program in silent mode for a little while; today we are ready to start blocking! A small number of the behavioral rules that we have will be updated to start blocking from today.
What does that mean for you?
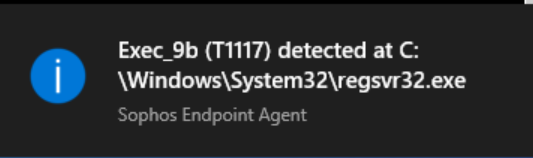
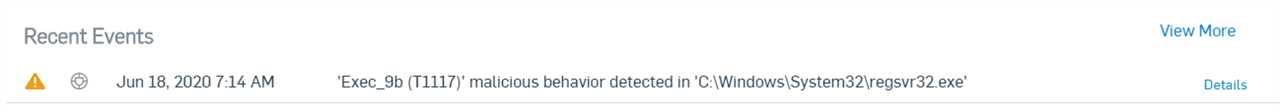
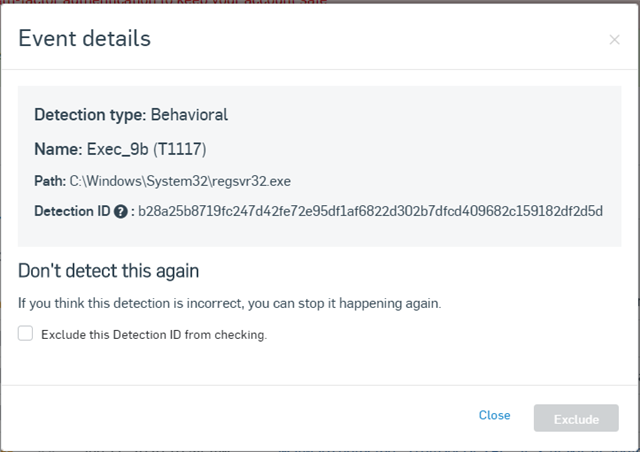
You might see some detections in Sophos Central and the local UI
What might you see?
What do you need to do?
Nothing really, post feedback here if you'd like. It'll be interesting to hear your experiences with this exciting new feature. We will be releasing more rules over the coming weeks.