This thread was automatically locked due to age.
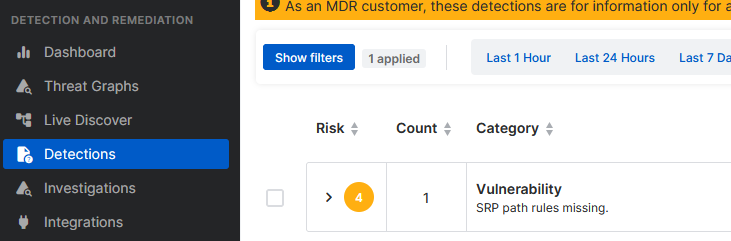
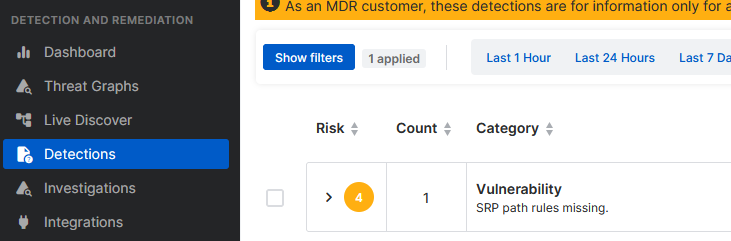
"detections identify activity on your devices that's unusual or suspicious but hasn't been blocked. They're different from events where we detect and block activity that we already know to be malicious." Sadly you dont get any information via support. The reason is simple, they want to sell MDR ;-)
After raising your concerns to our teams internally, I was informed that the detections related to Software Restriction Policies will be disabled in an upcoming release.

That is very good news, thank you.
We do understand that when looking at the 'detections' we're kind of looking "under the hood" of the Sophos engine and many detections are just observations (like a changed user, password incorrect, etc) and are mainly for MDR purposes. But, especially with the new user friendly dashboard graphs, end users can also keep a better eye on their environment (even those with MDR). If these 'medium' alerts will be gone (or informational) in the future, the view will be so much clearer.
Thanks!