Hi,
Something interesting has been happening while using the DPI Engine, I've found this happens sometimes after an user accidentally tried to download a malware and managed to do it.
Sometimes the DPI Engine doesn't hold the last packet, and let the user to download the file entirely, apparently without AV scan.
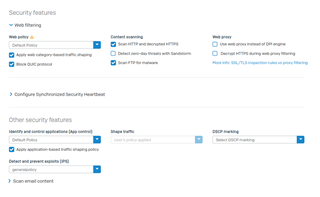
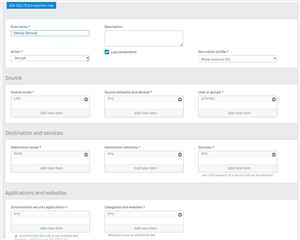
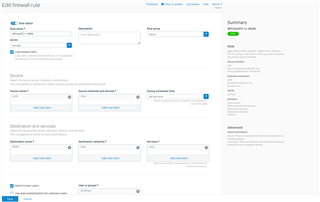
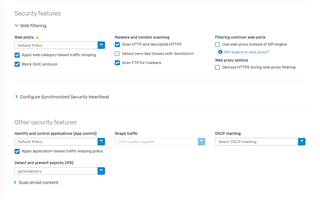
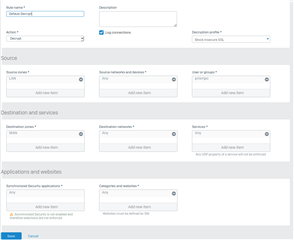
Here's the Rules I've used to test on my computer:
And here's a video of it happening with the standard Eicar file test.
After downloading it entirely for the first time, trying for a second time will throw you a notification, as it's supposed.
The interesting part, It never happens on a HTTP connection, only on HTTPS.
Is this a mistake on my part? or it's already known? This is happening since when v18 EAP 1 came out.
Thanks,


If you have a parsing error when this occurs then the response body is not scanned. If the body contains a virus then the virus may be downloaded.
Why we are randomly getting parsing errors, we still need to determine. No ETA.