The XG Firewall v18 Early Access Program (EAP) 3 Refresh-1 firmware release is now available for download!
If you've already registered for the v18 EAP and upgraded your XG Firewall to any of the older v18 EAP firmware, there's no need to re-register to gain access to the v18 EAP 3 Refresh-1 release. You will see a notice in the firewall UI to upgrade through the Up2Date service.
- New EAP registration and download for v18 EAP is NOW enabled. To get the latest release, go to the XG Firewall v18 EAP page.
- We've updated the "Known Issues, Advice for Users, and Incomplete Features" document with new information.
Please remember, this is still an early build of the v18 release so there are some things we’d like to bring to your attention before you download the firmware and begin testing it.
- We’ve attempted to make the build as bug-free as possible, however as is the nature of early access firmware we cannot guarantee it will be.
- We have released Memory optimization and Performance improvements in EAP 3 Refresh-1, still, the firmware is being tuned for performance. Expect to see faster speeds in future builds.
New Features and Highlights in SFOS v18 EAP 3 Refresh-1
- Route Based VPN
- Simplifies VPN policy creation with larger/dynamic networks.
- Network topology changes don’t impact IPSec VPN ‘policy’
- Also interoperates with non-Sophos route based VPN tunnels
- Configure IPSec using "Tunnel Interface" connection type listening on WAN interface. And assign IP to auto-created XFRM Interface. And configure routing (Static, Dynamic, SD-WAN PBR), firewall and NAT rules as required
- IPSec and MPLS can now be active at the same time, use RBVPN in SD-WAN policy routing
- NAT Improvements addressing early feedback we received from the Sophos Community
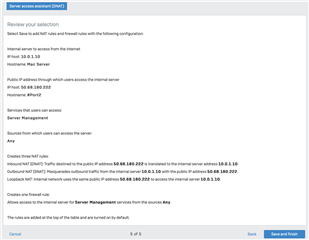
- Server access assistant (DNAT): Destination NAT assistant (or wizard) enables workflow to publish an internal server over internet in a few clicks
- More info below
- Default SNAT rule at the bottom of the NAT rule table that MASQ traffic going out of WAN interfaces.
- There is an open issue in Refresh-1 that turns on the default rule post migration. For No-NAT environments, please manually disable this rule to maintain the behavior.
- NAT rule UX placement is now consistent with firewall UI
- Server access assistant (DNAT): Destination NAT assistant (or wizard) enables workflow to publish an internal server over internet in a few clicks
- Flow monitor UX fixes
- Stability fixes for handling large number of live connections
-
Corrected sorting on BW columns (Retaining the sorting on refresh is still open - planned for next release)
- Negative Value in Upstream/downstream Bandwidth column
- Same Upload and download values when data is grouped by Source IP address/User
- Memory optimization and Performance improvements
- Option to restart wireless access points from XG v18 web console
New NAT Wizard
XG Firewall v18 introduces a new more powerful and flexible NAT implementation that has more in common with the approach being used in many other firewalls.
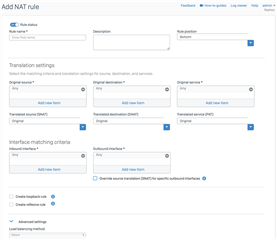
XG Firewall now features a dedicated NAT rule table that is traversed from top to bottom. While linked NAT rule options still exist for organizations that appreciate that simplicity, you can now create source, destination or full NAT translation in a single rule that offers more power, flexibility and visibility.
What's new in this Refresh of EAP3 is the result of extensive partner and customer feedback and consultation. The team has enhanced the layout to the NAT rule creation screen and also added a convenient and easy wizard to create complete server access rules. These additions - as well as embedded help content, makes this new feature much easier to use and enables everyone to make the most of this powerful new capability.
Here's an overview of the new enhancements to NAT in v18
- A new video guide on how to use the new NAT capability is built-in to the new NAT rule tab:

- New more intuitive layout to the NAT rule screen:
- New easy-to-use Wizard to create server access NAT rules with just a few clicks:
Important Issues Resolved in SF v18 EAP 3 Refresh-1
- NC-53500 XGFW interferes with certain SSL website connections
- NC-53016 Email Blocked Senders cannot be updated
- NC-52641 IPS Service getting DEAD
- NC-53228 Continuous receiving 'daemon.debug /bin/smcroute[6387]: Debu: 28 byte IGMP signaling dropped" in syslog.log
- NC-54038 Wrong notification message displayed after disabling firewall rule
- NC-52090 LogViewer: "Action is not Allowed" filtering not working in detailed view
- Flow monitor UX fixes
- + 150 issues and stability fixes are part of EAP 3 Refresh-1
Getting Started
Once you’re ready to go, we’ve got some great resources to help you get started:
- Recommended Reads - Check out these important forum posts
- “What’s New in v18” – See the complete feature list with descriptions
- v18 Interactive training course - Enroll in this interactive training course to learn more about v18
- v18 Admin Guide - Read the latest admin guide for v18
- v18 Evaluation Guide Slides – Learn about the features we’d like you to test
- v18 Public Release Notes – Read the latest notes about the v18 build
- v18 Known Issues and Limitations – Get updated information on any known issues, advice for users and incomplete features in v18
Things to Know Before Upgrading
Before upgrading to v18 EAP 3 Refresh-1 from an earlier version, there are a few things to note:
- You can upgrade to v18 EAP 3 from v17.5 MR6 or later MR versions of v17.5 including latest MR9; as well as from any earlier v18 EAP.
- Rollback (firmware switch) is supported as usual. You can roll back to v17.5 MRx if you experience any issues during the v18 EAP. As an example, the active firmware on the firewall is v18, and the second firmware version is v17.5. Administrators can switch between these two and the configuration on each will stay as it is.
- Backup and restore are supported as usual. SG Firewalls running SFOS, Cyberoam firewalls and XG Firewall backups can be restored on v18.
- Due to a minimum memory requirement of 4GB of RAM, XG 85 and XG 105 models cannot upgrade to v18 and must remain on a 17.x version.
- v18 firmware is not supported on Cyberoam models. However, Cyberoam firewall backups can be restored on an XG Firewall running v18.
- Downgrading from v18 to older firmware - using v17.5 or earlier firmware file - is NOT supported. The Web console will the give appropriate message. v18 uses Grub boot loader. The changed bootloader cannot recognize v17 firmware. Administrators can still use the hardware ISO of v17.5 or an earlier version to get the firewall on an older firmware version and restore the downgraded firmware's backup.
Recommended upgrade process when you test multiple v18 early access releases:
- This is applicable if you have upgraded to v18 from v17.5. When you further upgrade from v18-EAP(x) to v18-EAP(x+1), you can first switch to v17.5 and upgrade from v17.5 directly to v18-EAP(x+1). From there, you can then restore the backup of v18-EAP(x). This way you will always have v17.5 firmware in your second firmware slot, and leave an option open to roll back to v17.5 if needed.
Support
- Please do not call the general Sophos Support Hotline for EAP issues.
- Troubleshooting support for EAP versions is handled solely through the online Sophos Community EAP Forums.
Share Your Feedback
Communicating your experiences with the v18 EAP firmware is crucial to its success, so we want to hear from you! Please share your feedback via the Sophos Community or through your XG Firewall’s feedback mechanism in the user interface.
Thank you for taking the time to test the v18 EAP release. We’re excited about all the new features this release will bring to Sophos XG users and we appreciate your help making it happen!
Sincerely,
Your Sophos XG Firewall Product Team



