On 18.0.1 MR-1-Build396.
The new NAT setup does not work. On v17, picking the gateway you wanted worked great.
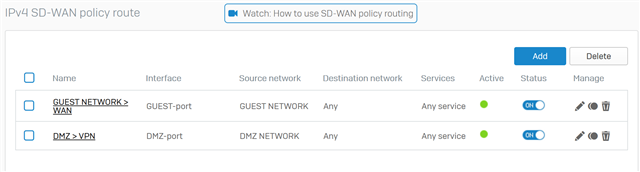
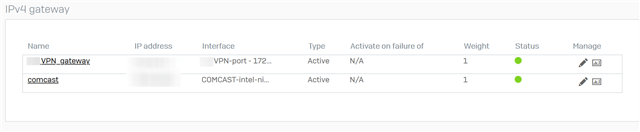
The gateway setup does not work. If the WAN gateway and VPN gateway have the same weight (as shown below), then the WAN stops working.
If I change the weight of the internet WAN gateway to 2 or more, the internet works again.
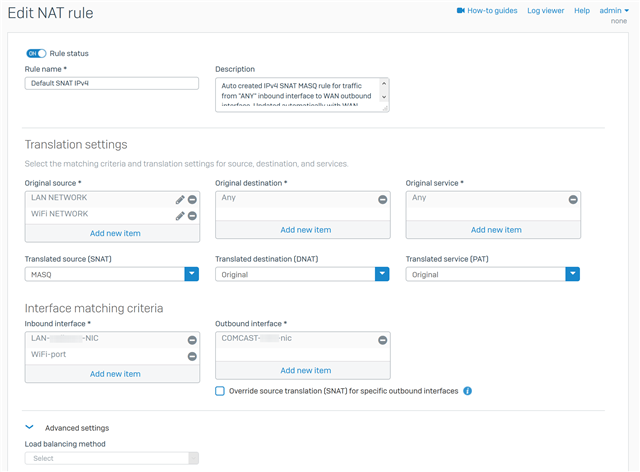
The default NAT rule only has the internet WAN link in it and not the VPN WAN link in it. This works when the gateway weights are not equal.
This NAT rule for the guest network DOES NOT WORK.
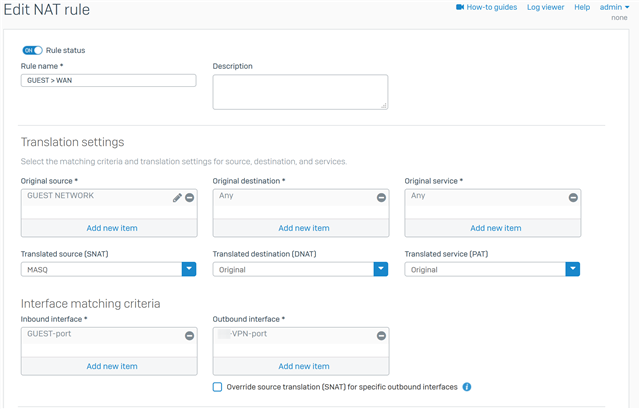
The only way to get NAT to work with a second WAN link (as shown below) is to create a linked NAT rule and then override SNAT for ONE specific host.
So how am I supposed to have a guest network with a separate WAN link?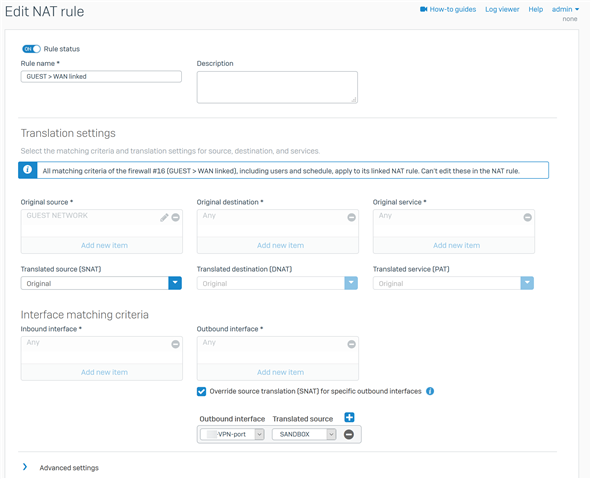
Thanks for listening.
EDIT 1:yes, there is a corresponding firewall rule in case you are wondering.
This thread was automatically locked due to age.