Help IPSEC VPN DISCONNECTS AND NOT ABLE TO AUTOCONNECT WHEN BRANCH SITE BOOT THEIR VPN ROUTER during MOrning
Helo , hope all is well, please help me on this concern ,
Scenario
-IPSEC VPN are disconnected when turnoff the BRANCH VPN ROUTER (CISCO RV SERIES) - Normal
-IPSEC VPN not autoconnect / established when the BRANCH VPN ROUTER is reboot / turnon
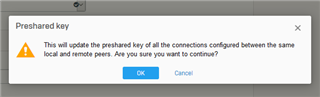
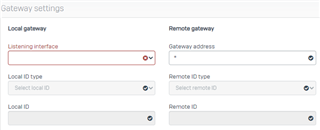
my work around is : RE ENTER THE PRESHARED KEY and the TUNNEL goes UP
But this is hassle everyday I refreshed the tunnel
This thread was automatically locked due to age.