Hi!
I'm having problem using new RED20 device + WiFi module.
With ethernet speed is just fine, but when connected to wifi connection speed is horrible.
RED's operation mode is Standard/unified.
Tested with various devices. Laptop connects to REDs AP at 300Mbps.
Most of the time Ping is well over 100. At worst over 3000ms.
What could be done to fix this? Firewall we're using is XG 210 running SFOS 17.5.11 MR-11.
Patterns are up to date.
Here's some pics:
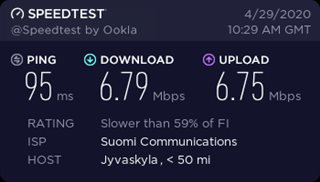
This is the speed with laptop connected to RED's wifi:
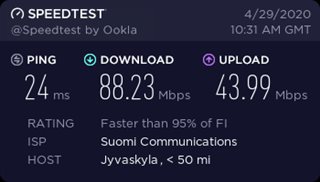
This is the result when connected with ethernet through RED:
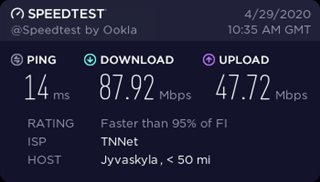
This is the Wifi speed when same device connected to APX320 to clarify it's not the client device issue (Not connected to RED):
This thread was automatically locked due to age.