I've recently gotten the XG and it was setup based on my old UTM by a third party. While I like that because it was setup quickly, I don't like it because I'm not as familiar with it as I'd like to be. That said, I'm really hoping I'm just doing something stupid, but I really can't figure this out and it's driving me crazy.
My network is setup that my primary LAN is port A1 (zone LAN) and hosts all of my Windows clients/servers/printers/etc in 10.21x.x.x networks. When we got the XG, we setup an additional 10.230.x.x network on port A4 (zone DMZ) specifically for our Chromebooks to get all of our inline filtering and other routing and such out of their way so they work better. Since we've done that they absolutely do work better in most cases. The thing that's puzzling me is getting some of the services from our regular network accessible to the Chromebooks, namely desktop monitoring software and local/non-cloud printing.
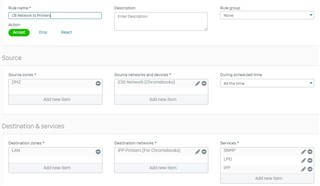
I created a couple of rules that I think should have done the trick, for instance here's rule 18 which is supposed to let the Chromebooks access the printers:
The problem is, when I enable this rule, they can't print. However, if I disable this rule, they can. I did a packet capture and when the rule is enabled, I'm getting an "INVALID_TRAFFIC" violation on rule 18, despite it seeming to match the ports and IP's I'm allowing. When I turn it off rule 0 applies and it allows everything. So two questions: Why doesn't my explicit rule work; and why does Rule 0, which I thought was a Deny All rule, allow it to work?
There are different IP's/ports involved but the same thing happens for the desktop monitoring rule.
Any help would be greatly appreciated!
This thread was automatically locked due to age.