Hi,
I'm new here and have the following problem.
I have checked it with Pre-shared key and also with certificate. The same results.
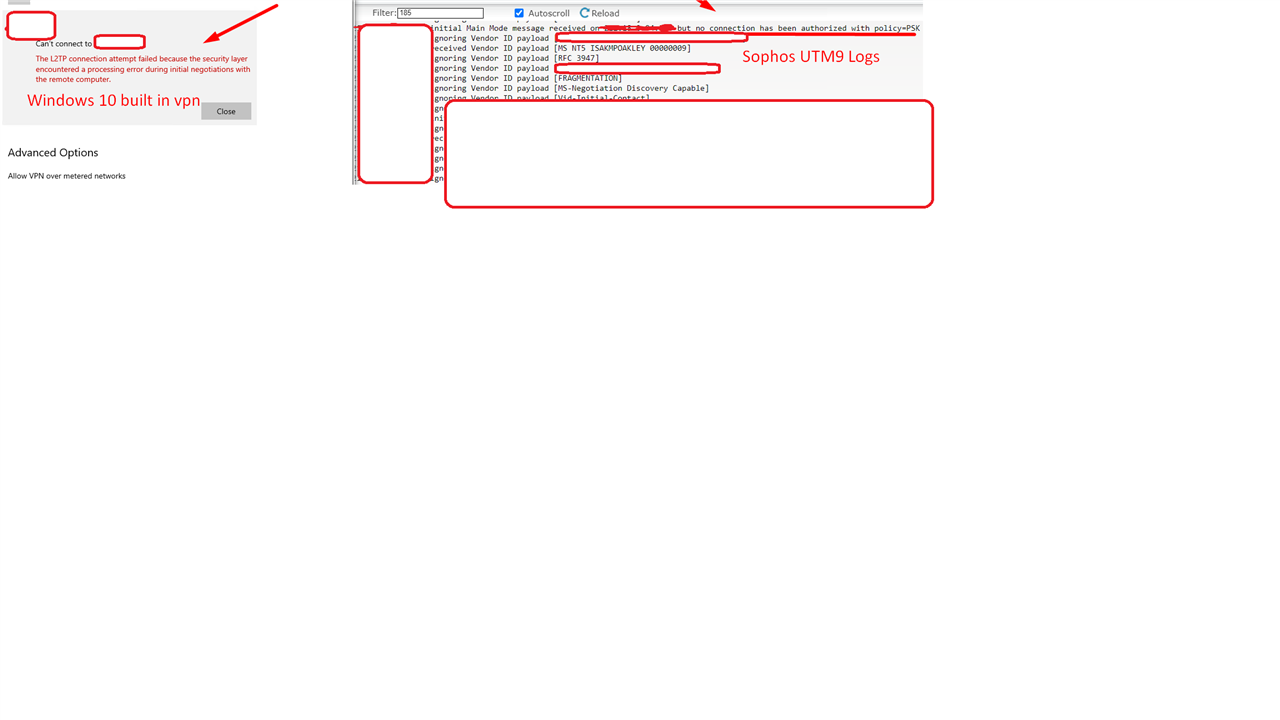
Does anyone has Info?
Thanks in Advance!
This thread was automatically locked due to age.
Hi,
I'm new here and have the following problem.
I have checked it with Pre-shared key and also with certificate. The same results.
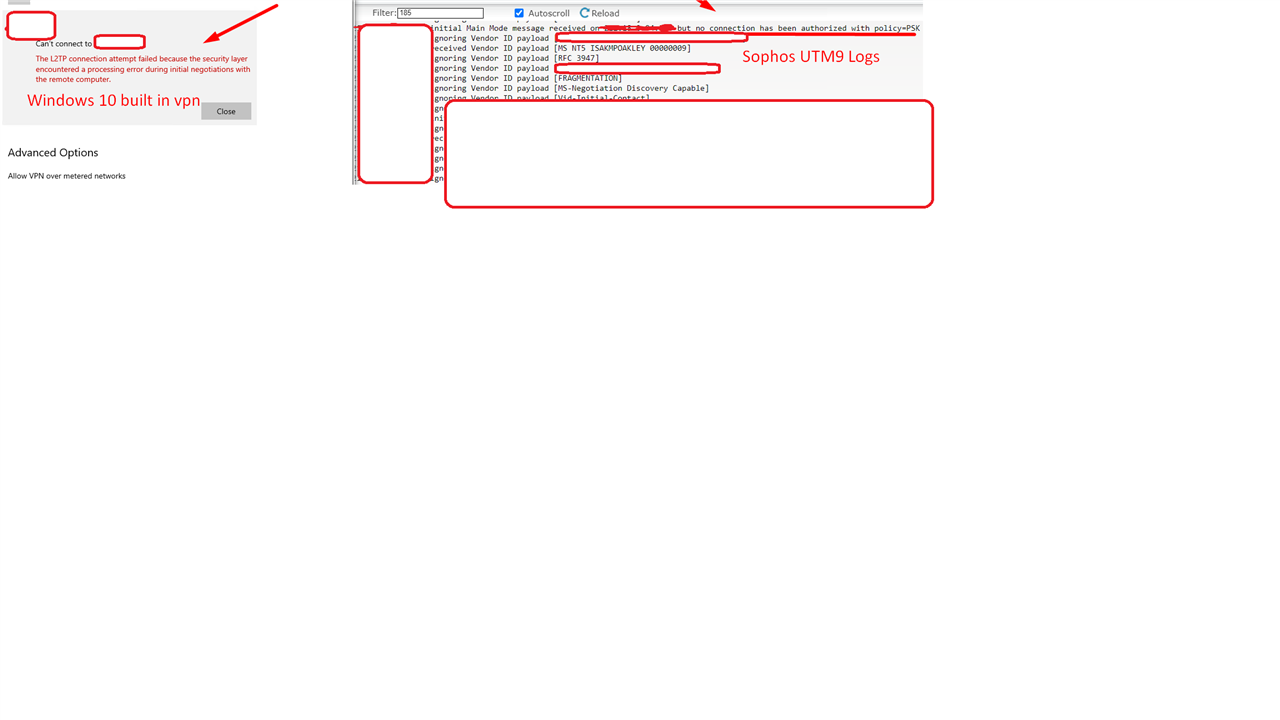
Does anyone has Info?
Thanks in Advance!
Hallo Avraam and welcome to the UTM Community!
Pictures are very helpful here when it's of the Edit of a configuration item. In the case of logs, it's better to copy and paste here from the log. If you prefer, obfuscate IPs like 84.XX.YY.121, 10.X.Y.100, 192.168.X.200 and 172.2X.Y.51. That lets us see immediately which IPs are local and which are identical or just in the same subnet. In this case, there's not enough information to help you until we see the results of what Harsh has asked for.
Cheers - Bob
Also, try with a very simple PSK like 1234 to see if you get the same message.
To correct a problem with Mac OS, one user changed the L2TP over IPsec IPsec Policy.
Cheers - Bob
PS There's no need for the SNAT
Hi,
Thanks for your Support.
I have changed from Uplink to the first Public Wan Interface,
I have got now the following logs.
______________With PSK__________________
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [01528bbbc00696121849ab9a1c5b2a5100000001]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: received Vendor ID payload [MS NT5 ISAKMPOAKLEY 00000009]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [RFC 3947]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02_n]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [FRAGMENTATION]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [MS-Negotiation Discovery Capable]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [Vid-Initial-Contact]
2021:02:18-15:53:42 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [IKE CGA version 1]
2021:02:18-15:53:42 utm pluto[24202]: "L_for admin"[7] * #173347: responding to Main Mode from unknown peer *
2021:02:18-15:53:42 utm pluto[24202]: "L_for admin"[7] * #173347: ECP_384 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
2021:02:18-15:53:42 utm pluto[24202]: "L_for admin"[7] * #173347: ECP_256 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
2021:02:18-15:53:42 utm pluto[24202]: "L_for admin"[7] * #173347: next payload type of ISAKMP Hash Payload has an unknown value: 129
2021:02:18-15:53:42 utm pluto[24202]: "L_for admin"[7] * #173347: malformed payload in packet
______________With Cert__________________
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [01528bbbc00696121849ab9a1c5b2a5100000001]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: received Vendor ID payload [MS NT5 ISAKMPOAKLEY 00000009]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [RFC 3947]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [draft-ietf-ipsec-nat-t-ike-02_n]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [FRAGMENTATION]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [MS-Negotiation Discovery Capable]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [Vid-Initial-Contact]
2021:02:18-16:52:49 utm pluto[24202]: packet from *:500: ignoring Vendor ID payload [IKE CGA version 1]
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: responding to Main Mode from unknown peer *
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: ECP_384 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: ECP_256 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: Peer ID is ID_DER_ASN1_DN: 'C=de, L=*********, O=********r, CN=l2tp_test'
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: crl not found
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: certificate status unknown
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: we have a cert and are sending it
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: sent MR3, ISAKMP SA established
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[2] * #173851: responding to Quick Mode
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[2] * #173851: IPsec SA established {ESP=>0x76655774 <0xc7ee960b}
Does it work with mac or ios ?
+
Do you followed this guide?
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: ECP_384 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
2021:02:18-16:52:49 utm pluto[24202]: "L_for admin"[3] * #173850: ECP_256 is not supported. Attribute OAKLEY_GROUP_DESCRIPTION
Please show a picture of the Edit of the "L2TP-over-IPsec" IPsec Policy.
Cheers - Bob
Does the client have these same settings for the 'IKE DH Group' and the 'IPsec PFS Group'?
Cheers - Bob