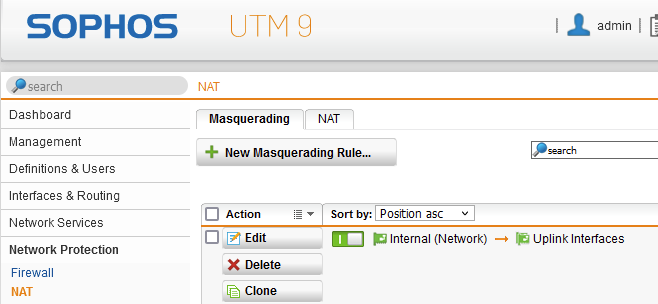
Newbie question. I am running Sophos Home UTM 9 software appliance on a server I built. I have an app running on a single workstation that needs to communicated in and out on ports 4000 and 4001. I set up the following rules but it doesn't seem to be enough or is misconfigured.
In Firewall rules I created
Rule 1 - Any(4/6) ---> Workstation TCP 4000 TCP 4001
Rule 2 - LAN --> Any(4/6) TCP 4000 TCP 4001
This app needs two way communication to servers hosted elsewhere and not on my network. Currently, if I try to telnet to those servers on ports 4000 or 4001, I get "connection failed" which tells me the ports are still not open.
This thread was automatically locked due to age.