Hi, on 9.707,
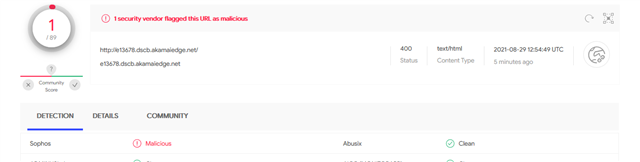
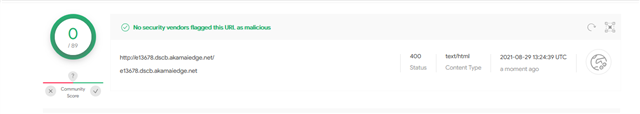
e13678.dspb.akamaiedge.net was flagged by the ATP system tonight:
2021:08:28-19:50:28 fw named[5536]: rpz: client 192.168.1.3#57698 (e13678.dscb.akamaiedge.net): view default: rpz QNAME NXDOMAIN rewrite e13678.dscb.akamaiedge.net via e13678.dscb.akamaiedge.net
Since Akamai is normally considered a trustworthy CDN, I need more information. What is the reason the traffic is suspicious?
Thanks,
Barry
(home user and commercial customer)
This thread was automatically locked due to age.