Auf einigen UTMs werden immer noch neue Let's Encrypt Zertifikate erneuert / neu ausgestellt mit der alten R3 / X3 Root Zertifikatskette.
Das heißt diese sind ab morgen nicht mehr gültig.
Deaktivieren und aktivieren von Let's Encrypt hilft hier nicht.
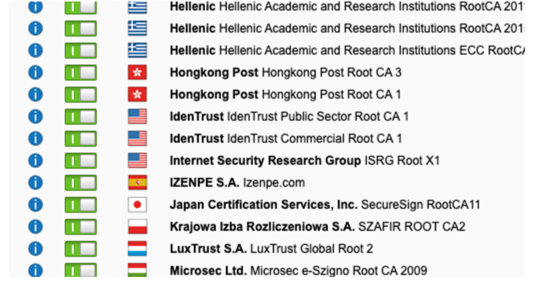
Weiß jemand, wie man die UTM dazu bringt auf das X1 Zertifikat zu wechseln?
Gruß Volker
This thread was automatically locked due to age.