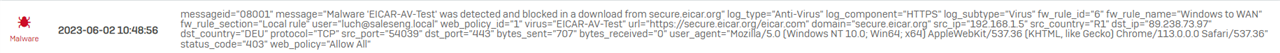
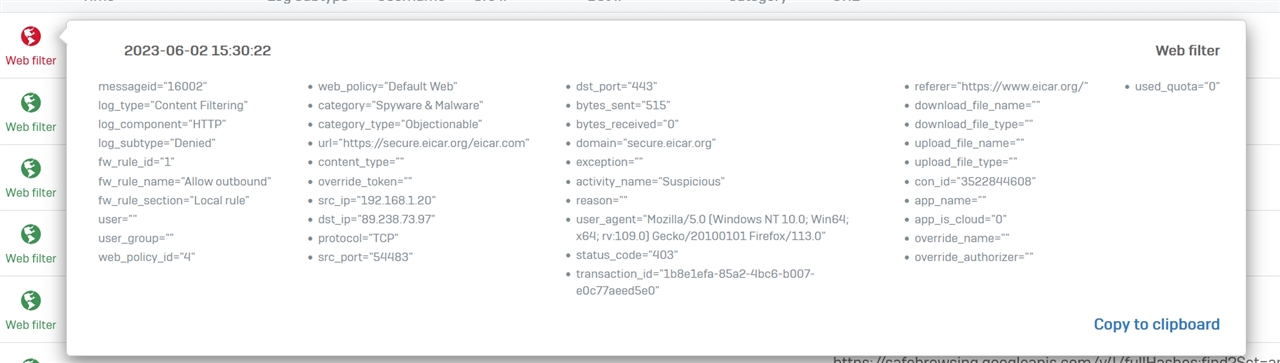
I performed the eicar test where I attempt to download the Eicar virus testfile. The block page shows that the file eicar.com was blocked by filetype. However, the webfilter log shows that the website was blocked, but does not specify that it was due to a fileype being blocked. HTTPS decryption is working properly, but I noticed it was different this time:
Usually the webfilter blocks the eicar testfile from downloading and the block page says it blocked "websites categorized as Malware".
This time the webfilter did not detect the eicar test site as a malware site but instead blocked the ".com" filetype from downloading and did not actually detect the eicar testfile as a virus. the other .ZIP files were blocked due to web category Malware, and not extracted and scanned by the antivirus.
Nowhere i
But the logs are frustrating, with many users complaining that the block page/log is not specific enough to let a system admin know enough about what the exact details of the block are caused by.
I looked through the logs (ATP, Zero-day protection, web filter), and there is no log anywhere that related to blocked filetypes.
I'ts even more strange since Sophos categorizes the Eicar testfile website as Information technology, Acceptable.
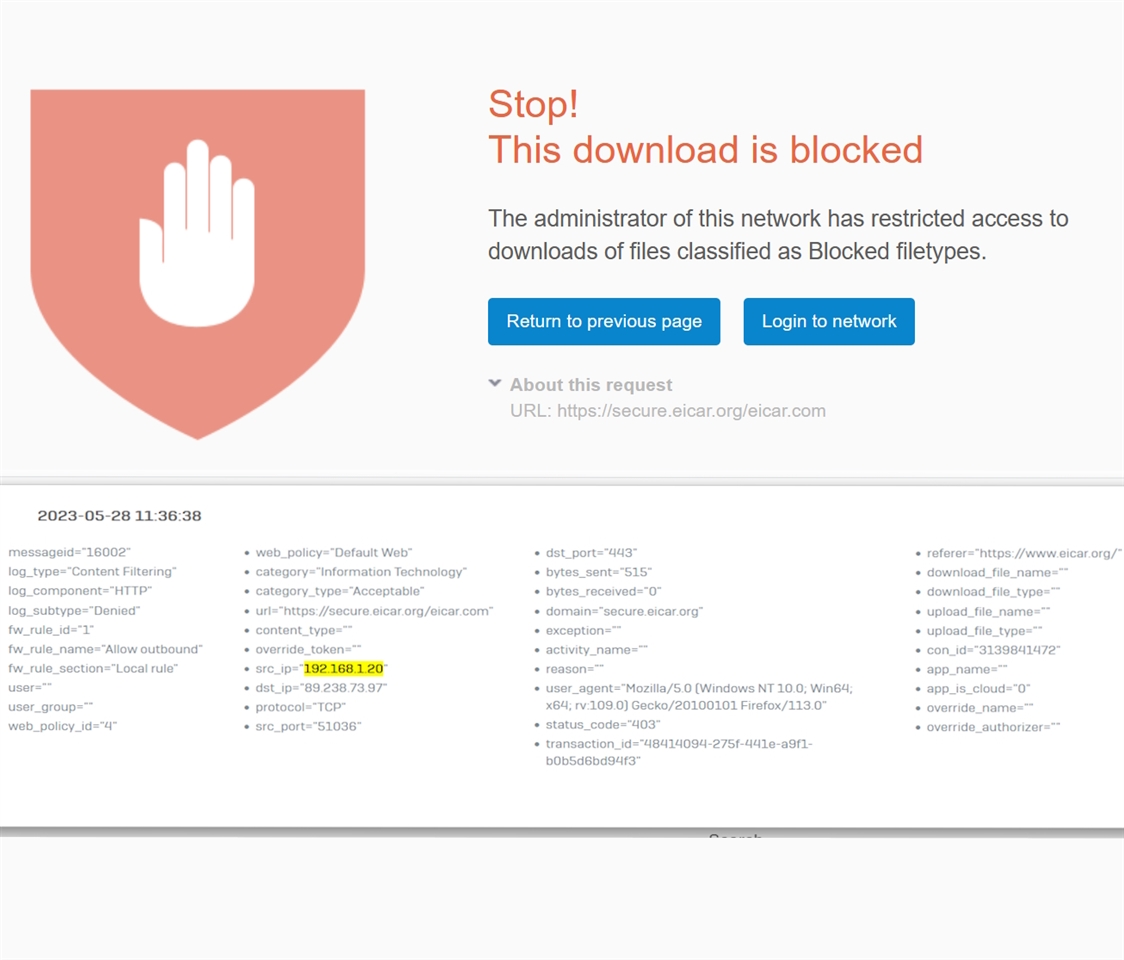
I created a Policy check exclusion for eicar.com in the Web Filter Exceptions, and now the AV component is able to successfully scan the .ZIP archives and detect them as malware. The eicar test files are now appearing in the Zero-Day protection logs as they should. If I remove the .COM filetype from the list of blocked filetypes, then it should also appear. This was just a configuration issue. But still, the log should say weather a download was blocked by filetype, since the eicar testfile site is categorized as acceptable, the log entry does not give any details to why it was blocked.
This thread was automatically locked due to age.