Hi,
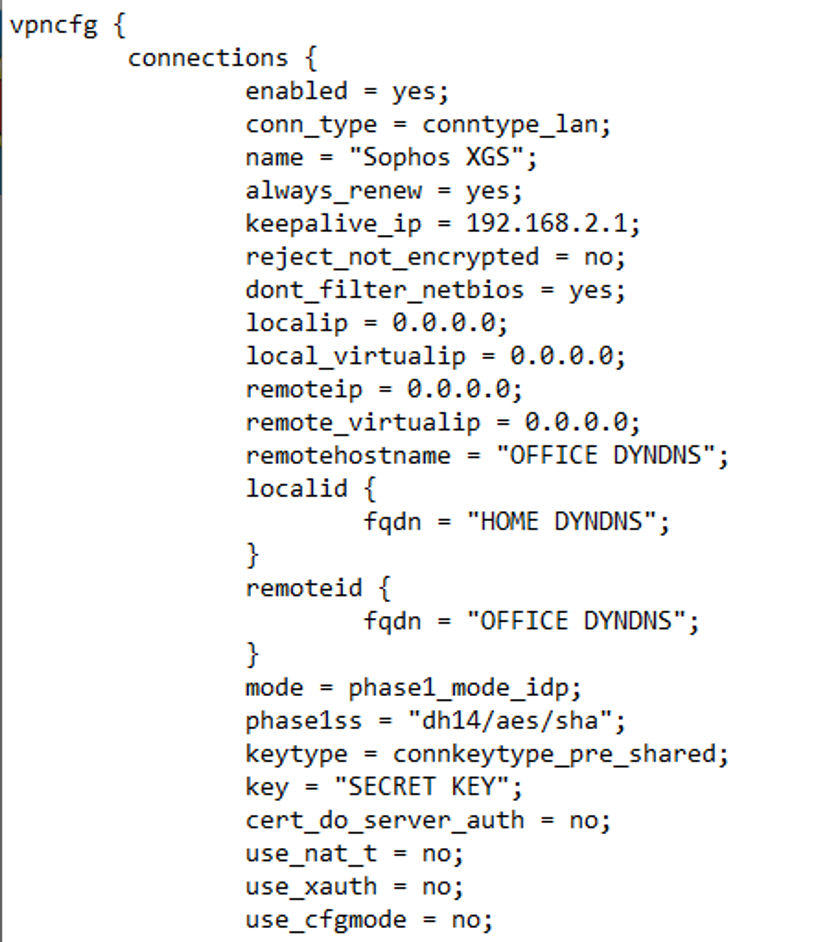
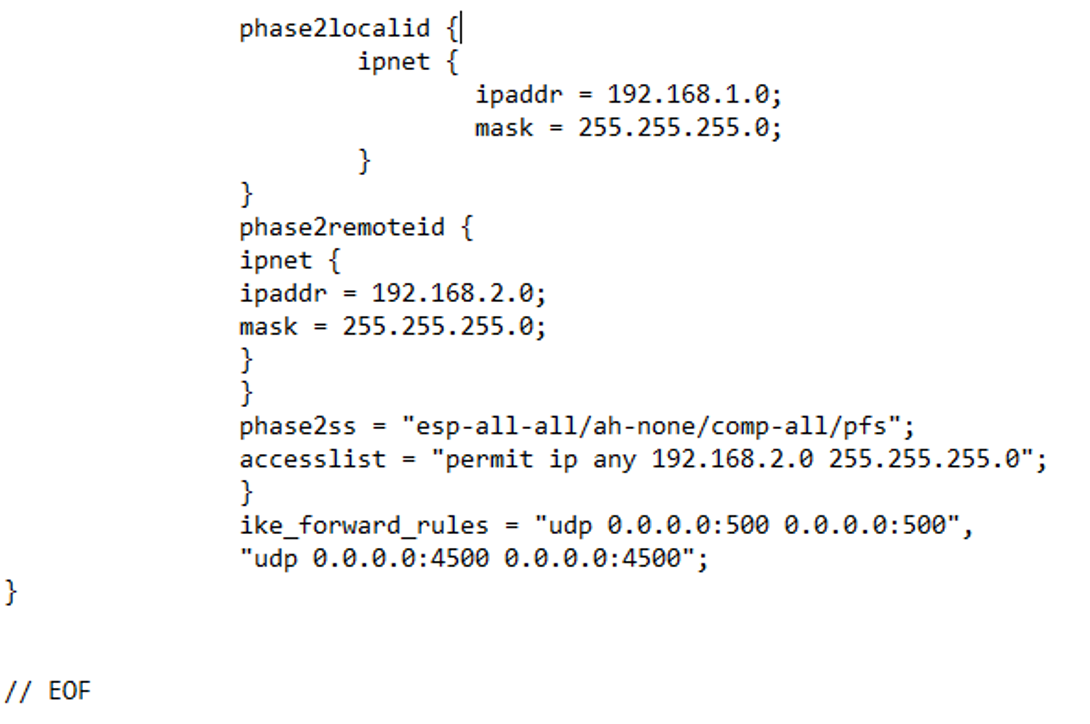
I just switched from the UTM to XGS.
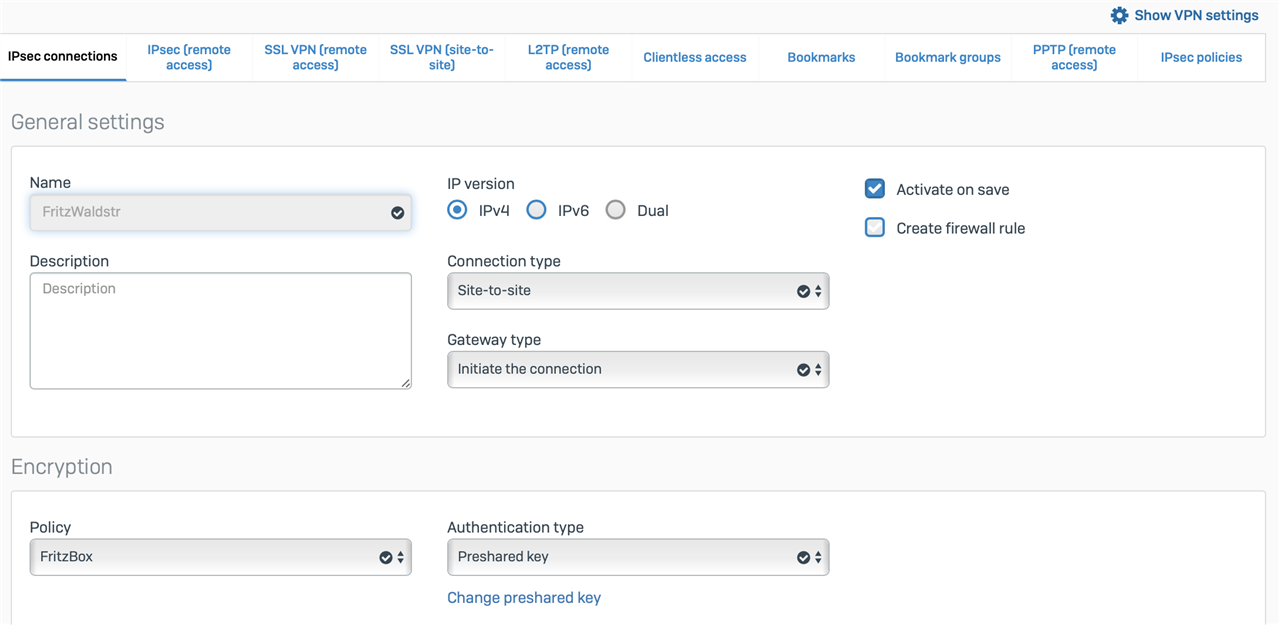
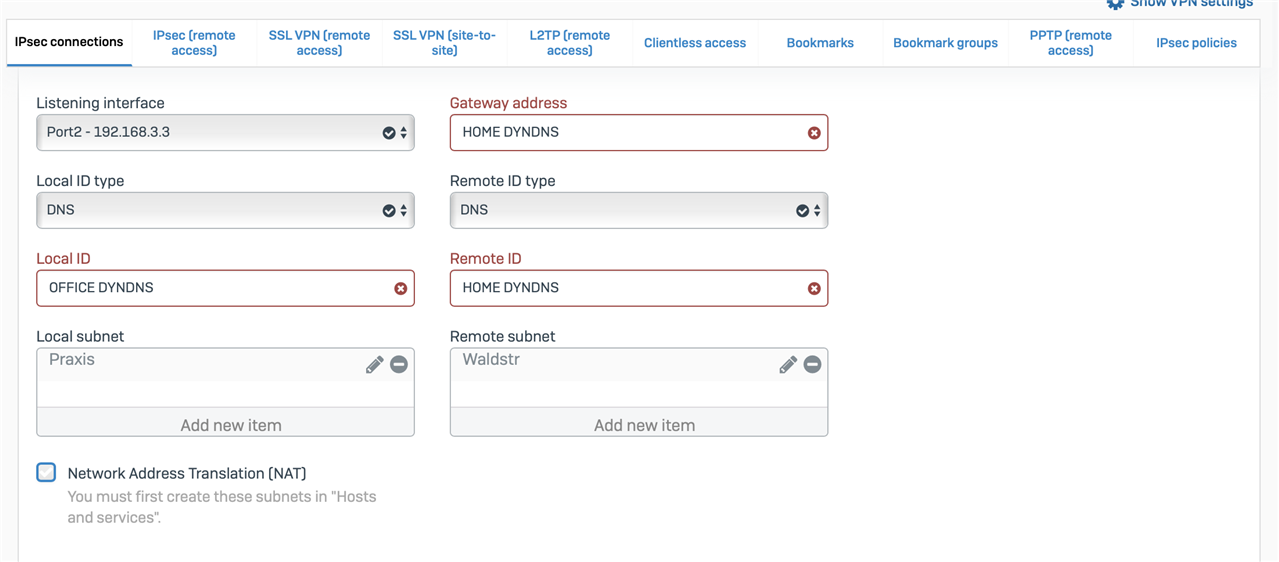
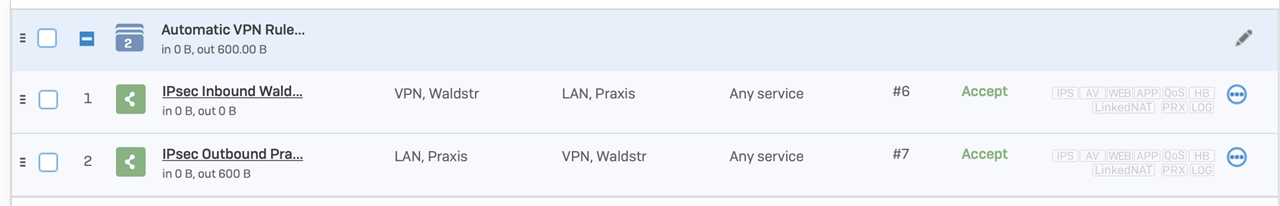
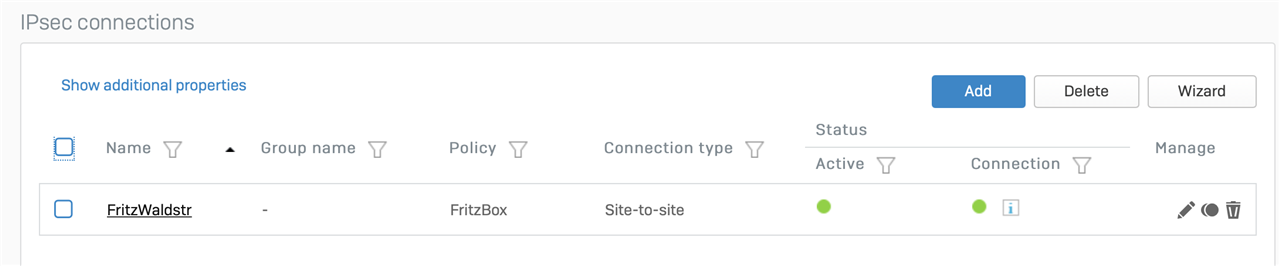
After some trial the IPSec connection is successfully established, tunnel shown green on both sides. Firewall rules auto created, but I also tried to create manual ones.
Unfortunately no traffic is possible between the two networks.
Looking at the Firewall rules there is Inbound traffic on the VPN Rule, but no Outbound.
Looking at Reports / VPN connection the issue seems to be that there is no "Local Gateway" available.
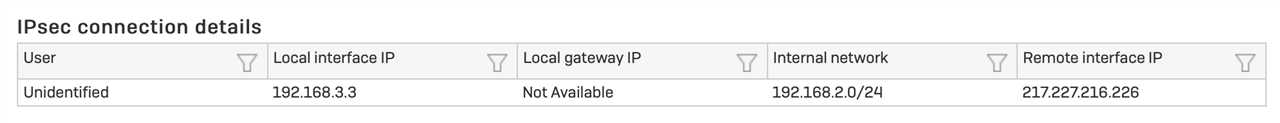
It's probably a small thing, but what do I need to configure besides creating the IPSEC connection and creating the firewall rules?
Thanks, Olaf
This thread was automatically locked due to age.