Hi folks,
recently my local CA expired and is now causing me grief on all my Apple devices using MAC mail.
The errors vary from not suitable for pinning to the site you are connecting to is unsafe or not recognised. The errors are affecting both SMTPS and Imaps. For the moment while I try to resolve the issue I have disabled smtps scanning.
I have tried to generate a new CA on the XG with a 12 month life similar to the one that expired except the export process does not work and the exported car is not recognised. I have tried renaming the CER, modified it settings but the same error persists. Also Iwhen exporting I see the encoded certificate displayed which all seems wrong to me.
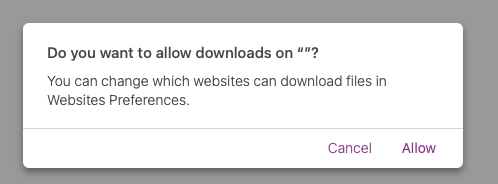
The export message is
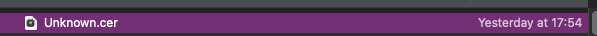
The exported file
The result is I cannot generate a local CA of any use.
Ian
This thread was automatically locked due to age.

