We have setup an XG 135 running v18 MR4. Default out of the box our Canon Copier with scan to email is blocked. This was working on the firewall we pulled out, so we know the scan to email settings are working. We are scanning to port 2525 using smtp2go.
I have searched far and wide on how to allow outbound SMTP. Either it is for an earlier version (v17 or earlier) and does not directly translate.
I have tried both MTA and Legacy mode
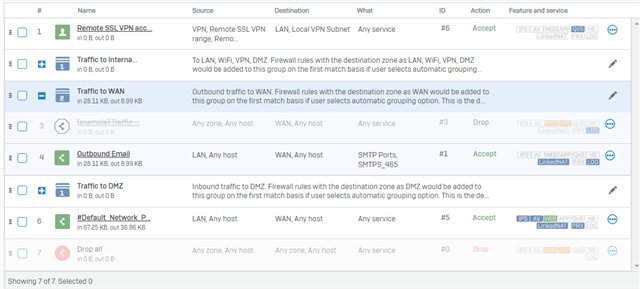
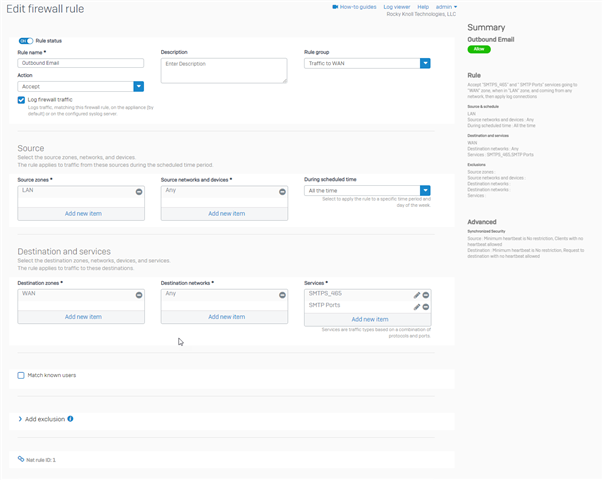
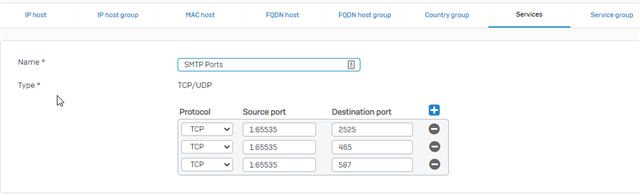
I have created a service group for ports 2525, 465, 587 and created a firewall rule for Traffic to WAN.
I have watched the logs and not seen anything of value to help me troubleshoot.
Does anyone have instructions on how to allow a single IP to send outbound email over port 2525?
Thanks
This thread was automatically locked due to age.