Hi .
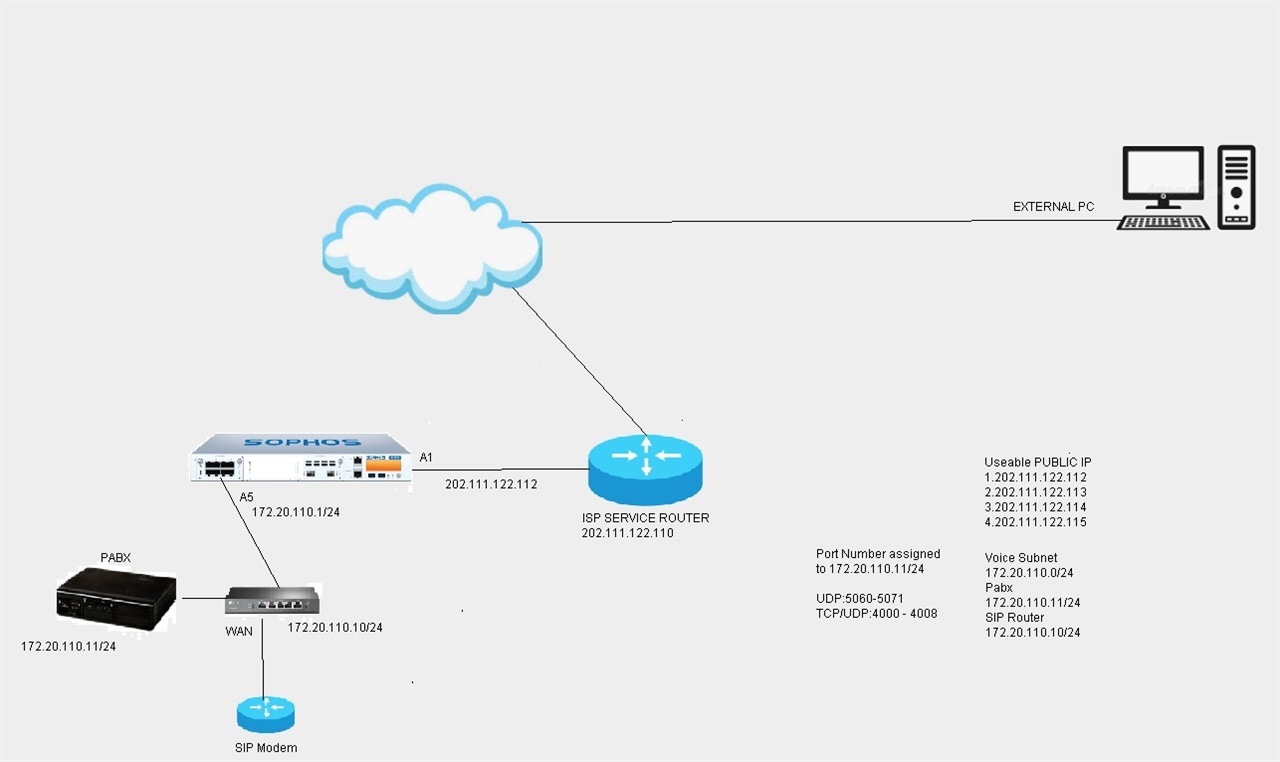
I'm having trouble trying to get one of the Public IP(Alias) to be nat onto voice subnet interface.
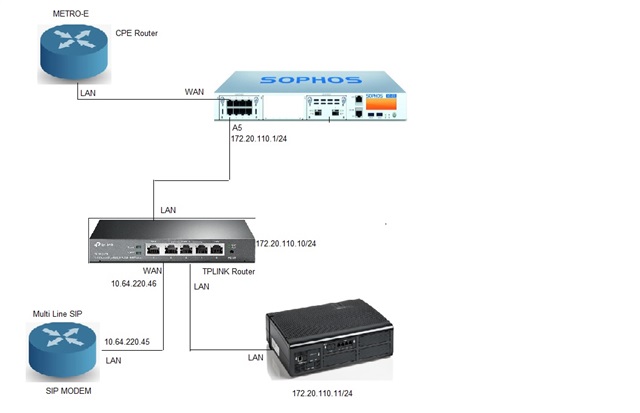
Here's the diagram below.
Network Diagram.
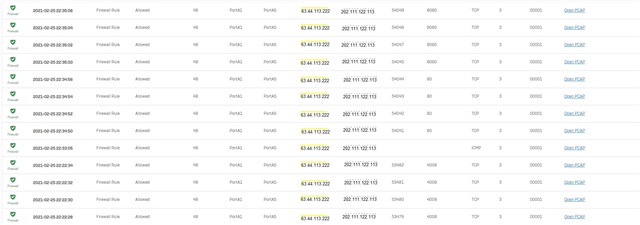
Here's what i configure for the Leased IP Line.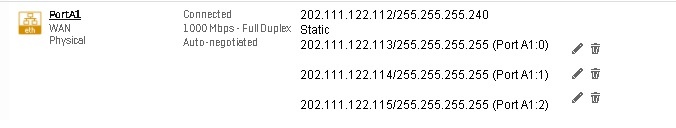
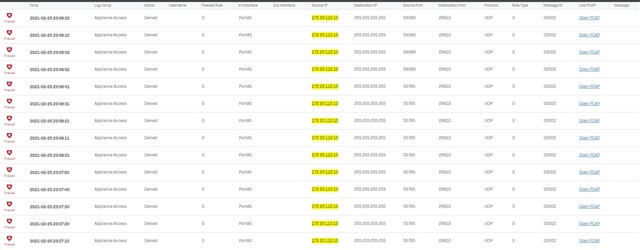
For voice LAN interface Subnet i configure as below.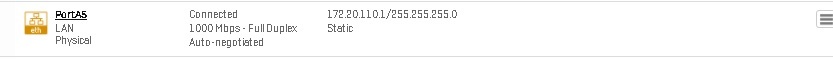
As for rule. I did it as below.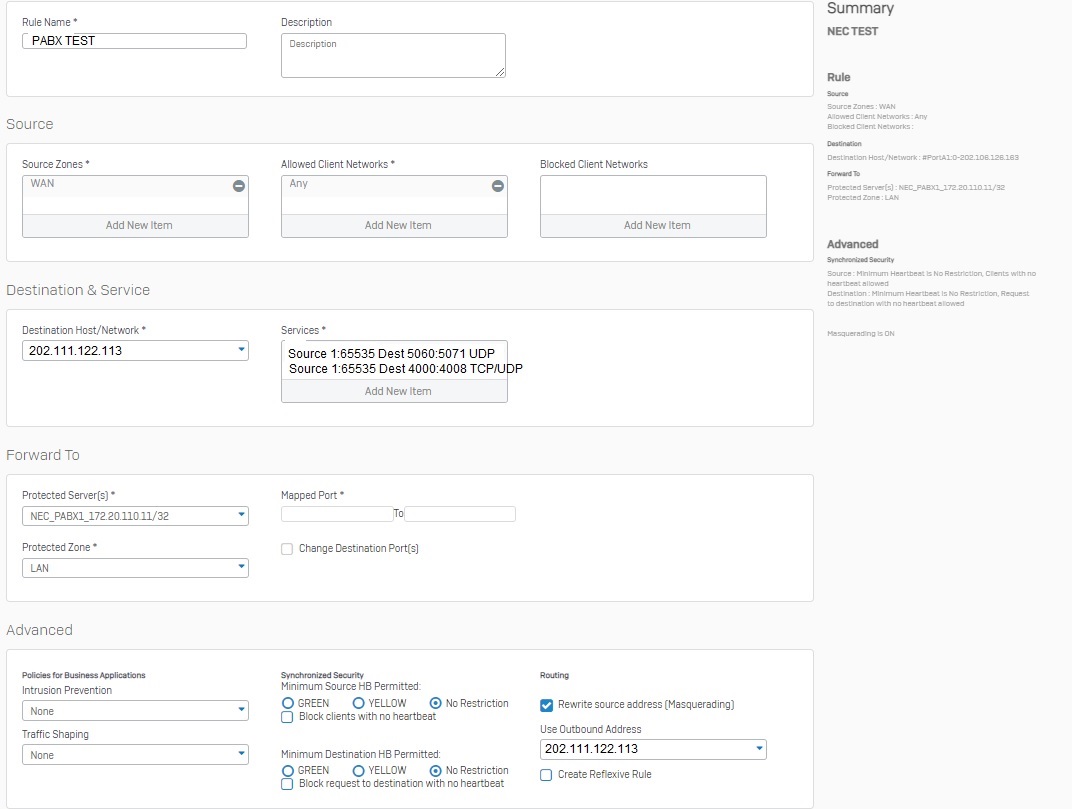
I have trouble reaching 202.111.122.113 via 4000 to 4008.
May i know which settings i did wrong or is there something i left out ?
This thread was automatically locked due to age.