Afternoon all. I'm a Sophos noob and have a question!
I have been tasked with using an SG210 as a WAN selector.
From e0 I'll have a connection to my core switch which hosts some VLAN's.
The Link from the core to the Sophos is routed so my default route on the switch is 0.0.0.0 0.0.0.0 192.168.199.1, the core switch IP address is 192.168.199.2 and this link is on VLAN 199
The core switch is the D/G for all the LAN's so LAN to Sophos should be a straightforward routing path.
I have created the appropriate routes on the e0 interface that point to 192.168.199.2
On e1, e2 and e4 I have different WAN routers.
e1 ip is 10.1.1.2 with the router connected being 10.1.1.1. Traffic is then NAT'd by this router to the outside world. e2 and e4 follow the same pattern except e2 is a DHCP addressing scheme.
The use case is this: The Sophos is on a ship. Sometimes it will be at sea using a VSAT internet service connected to e1. Sometimes it will be docked using a harbour supplied shore-lie on e2 and sometimes it will be close to shore and using a 3g/4g router on e4. The crew (who will be trained) need to be able to log in to the Sophos, choose the appropriate WAN connection and have traffic flow. They will not want to load balance at all, they just need to be able to get internet down whatever link is most appropriate at the time.
I am having trouble making this work. I am more used to Kerio devices which make this a breeze (because they are designed as WAN selectors) and I am fairly handy with Cisco CLI too. I've spent a good while at this searching the internet and the forum for answers to no avail. I'm looking for as minimal configuration as possible to keep complication down and to try to make any fault-finding easier should there be issues arising in use.
I am hoping the attached diagram helps with the explanation.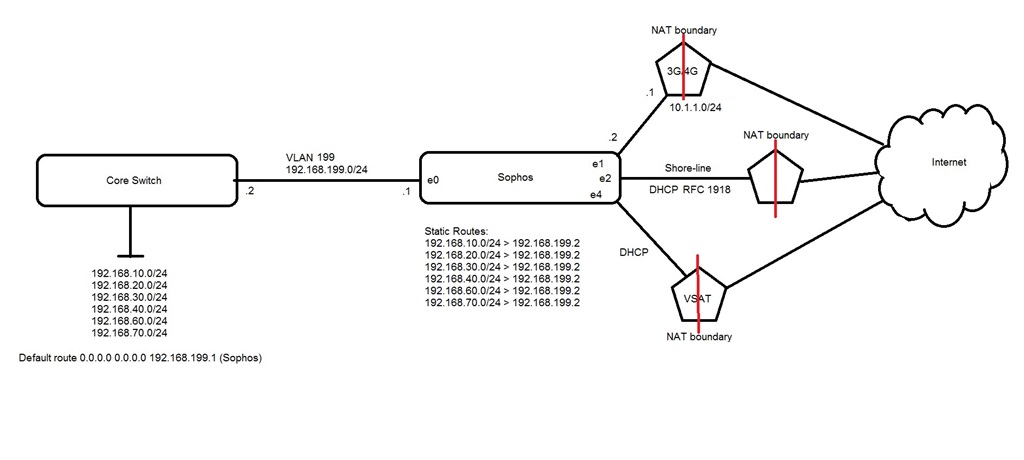
This thread was automatically locked due to age.



