Hi All,
We have UTM 9 and firmware version is 9.603-1. We have established a VPN connection to Azure. We have already one other connection to our branch We could not find the reason but it starts to give duplicate message problems and then the connection is dropping with Azure. It happend every 2-4 days.
2019:07:10-15:18:45 utm pluto[6401]: "S_REF_IpsSitAzure_0" #397: Quick Mode I1 message is unacceptable because it uses a previously used Message ID 0x01000000 (perhaps this is a duplicated packet)
2019:07:10-15:18:45 utm pluto[6401]: "S_REF_IpsSitAzure_0" #397: sending encrypted notification INVALID_MESSAGE_ID to 168.63.44.99:500
2019:07:10-15:18:45 utm pluto[6401]: "S_REF_IpsSitAzure_0" #397: Quick Mode I1 message is unacceptable because it uses a previously used Message ID 0x02000000 (perhaps this is a duplicated packet) 2019:07:10-15:18:45 utm pluto[6401]: "S_REF_IpsSitAzure_0" #397: sending encrypted notification INVALID_MESSAGE_ID to *:500
If vpn is working , there is no error message and everthing is working fine.
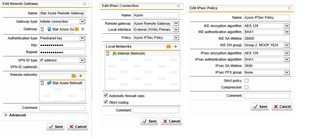
We are using policy based routing and we have tried to connect with Route based policy with Azure we could not connect the Azure. Microsoft says that, Route based policies are much stable compared to policay based route.
Can somebody suggest some resolution for this ? Thanks in advance.
Sedat EU
This thread was automatically locked due to age.