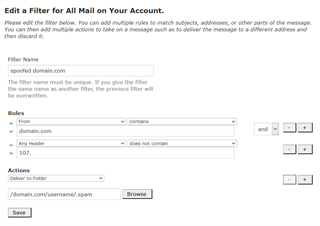
hy ,
how can I block this kind of mail in sophos
"" *********has been hacked, change your password ASAP
Hello,
As you may have noticed, I sent this email from your email account (if you didn't see, check the from email id). In other words, I have fullccess to your email account.
I infected you with a malware a few months back when you visited an adult site, and since then, I have been observing your actions.
The malware gave me full access and control over your system, meaning, I can see everything on your screen, turn on your camera or microphon and you won't even notice about it.
I also have access to all your contacts. ""
best regards
This thread was automatically locked due to age.