Hello,
I've been bashing my head against this issue for a few days and finally need to ask for some help. I have a network created in AWS which uses a Sophos UTM for all connections into the VPC. I'm not using the AWS VPN Tunnel for VPC.
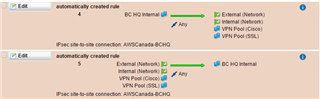
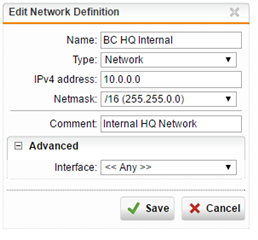
The Sophos is connected to our SonicWall in the HQ using a Site-To-Site IPSec tunnel and all connections are up on both sides. Traffic is flowing no problem. The issue occurs when i try to send RADUIS authentication traffic from the HQ to the VPC in AWS through Sophos. I cannot see any traffic on the sophos side.
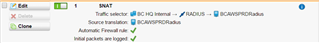
I created a SNAT rule on the sophos. The Firewall Logs show the traffic hit the Firewall. But still no traffic hitting the Server through Sophos.
Note: If i connect the AWS tunnel to my firewall in the HQ the radius traffic works... its only when going through the Sophos.
This thread was automatically locked due to age.