Dear kind users,
I feel super dumb asking this question but I can't seem to find how to do this or where it is described.
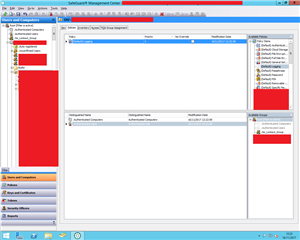
I am evaluating the SafeGuard Encrytpion solution for my company with a trial license and I'm seem to be unable to apply rule/rulesets to Active Directory users groups or computers
I haven't found any ressources with screenshots or detailed explanations on how to do this and I appreciate any pointers in the right direction.
Kind Regards
This thread was automatically locked due to age.